Since I forgot to branch the original source, the branching looked awesomely crappy. Therefore I decided to rebase entire thing to ease up keeping track with Moebooru “mainline”. All my commits are now in branch “default”. If you didn’t do any change, backout up to revision 9174b6b5b02d and then pull again. And then, don’t ever touch moe branch again anymore.
Monthly Archives: March 2012
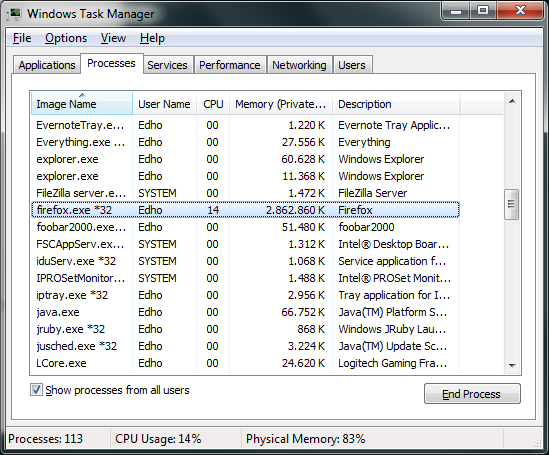
Firefox Memory Usage
moebooru again
Last week I posted about my random project which involves modernizing moebooru without doing complete rewrite (see this for yet another complete rewrite attempt).
Let’s revisit the plan:
- Upgrade to Ruby 1.9: done, need testing.
- Update all plugins: mostly done, can use some trimming.
- Update anything deprecated: nope
- Migrate to Bundler: done, not sure how to test.
- Use RMagick instead of custom ruby-gd plugin: nope
- Use RMagick instead of calling jhead binary: nope
- And more!: I hope you didn’t expect me to do more while there are incomplete items above.
Sure looks good. Need more testing though. There’s also one part which I totally had no idea why should be changed when upgrading to 1.9. Just grep for FIXME to see which it is and hopefully fix it up for me (or explain what it does).
As usual, having completed the work for today, live demo is up and open for everyone to break (…if there’s anyone, that is).
[ Live Demo | Repository ]
bcrypt in Debian
WARNING: using method below will lock yourself out when using emergency console since whatever crypt it’s using surely doesn’t understand bcrypt (as I experienced myself). Additionally, this solution won’t add bcrypt support to other applications using crypt interface like proftpd unless it’s started by preloading libxcrypt.so first (also from my own experience).
As much as Drepper want to pretend bcrypt is wrong solution, it actually gives one benefit: ease of switch to Linux. Some systems use bcrypt by default or configurable to use it. On other case, there might be time where you need system’s (or applications using system’s) crypt to handle bcrypt passwords from external system (usually web applications).
It’s quite difficult to enable bcrypt support in RHEL based distro as there is no libxcrypt and pam_unix2 packages available. Thankfully it’s available in Debian (and derivatives) in package libpam-unix2.
The README.Debian says to modify files in /etc/pam.d but if I remember it correctly, it confused apt PAM handling system or whatever. Fast forward few weeks, I discovered a better way to use it by creating PAM configuration in /usr/share/pam-configs. Since it’s mostly equivalent to normal pam_unix, I just copy and modify the file using this (long-ass) oneliner sed:
sed -e 's/pam_unix.so/pam_unix2.so/g;s/^Name: Unix authentication$/Name: Unix2 authentication/;s/pam_unix2.so obscure sha512/pam_unix2.so obscure blowfish rounds=8/;s/ nullok_secure//' /usr/share/pam-configs/unix > /usr/share/pam-configs/unix2
Then execute pam-auth-update, select Unix2 authentication and deselect Unix authentication. Don’t forget to update passwords for all other users as well or they won’t be able to login since pam_unix2 doesn’t recognize sha based hashes.
Actually, change all other users password to use md5 first before replacing the PAM with pam_unix2.
Update 2012-04-01: Removed nullok_secure since it isn’t supported.
Update 2012-06-09: Added warning.
FreeBSD is Rolling Release (the ports)
Don’t get tricked by the “release” system. Apart of the base system, FreeBSD perfectly qualifies as rolling release. I guess it’s also why the binary package management sucked so badly. You won’t find how to upgrade certain packages using binary method in their Ports’ UPDATING page.
Here’s the example:
20120225: AFFECTS: users of archivers/libarchive AUTHOR: glewis@FreeBSD.org libarchive has been updated to version 3.0.3, with a shared library bump. This requires dependent ports to be rebuilt. # portmaster -r libarchive or # portupgrade -r archivers/libarchive
You would think the dependent packages got version bump to ensure their proper dependency – but they didn’t. Instead you had to recompile everything depending on it.
And then there’s another case:
20120220: AFFECTS: users of graphics/libungif AUTHOR: dinoex@FreeBSD.org libungif is obsolete, please deinstall it and rebuild all ports using it with graphics/giflib. # portmaster -o graphics/giflib graphics/libungif # portmaster -r giflib or # portupgrade -o graphics/giflib graphics/libungif # portupgrade -rf giflib
Of course, ArchLinux kind of managed to do it but that’s a purely binary rolling release Linux distro. The maintainer worked hard to ensure such kind of thing get handled properly by all their users which mostly use binary packages. FreeBSD on other hand tried to claim capable of both but it really isn’t (unless I missed something).
I’m intending to contact pkgng creator to ask his opinion about this but have yet to do it…
Removing Annoying Speaker Static Noise
I’m not sure which sound cards are exhibiting this problem but at least it is in my system (onboard Realtek HD – Intel DH61BE motherboard running Windows 7 x64). It’s been annoying me since like forever and finally tonight I decided to actually solve the problem.
As it turns out, the solution is quite simple: disable PC Beep channel. A quick google showed this hit quite a bit of people and apparently this is the reason (or at least related).
On related note, apparently I’ve did this before and then completely forgotten. This is why I wrote it this time.
Manga Collection
An Attempt to Update moebooru Engine
If you didn’t know, the current moebooru running on oreno.imouto is using ancient version of many things. It also uses a custom lighty module (mod_zipfile) which doesn’t seem to be available anywhere.
I’ve updated it with latest Rails 2.x and made it compatible with nginx. Mostly. You can see it running here.
The plans:
- Upgrade to Ruby 1.9.
- Update all plugins.
- Update anything deprecated.
- Migrate to Bundler.
- Use RMagick instead of custom ruby-gd plugin.
- Use RMagick instead of calling jhead binary.
- And more!
We’ll see if I can actually finish this one. Grab the source here. Yeah, I’m using Mercurial for a Rails project.
nginx – gzip all the text
During my migration to other server, I recreated some of my configs and enabled gzip compression for most file types. Here’s the relevant config:
gzip on; gzip_vary on; gzip_disable "msie6"; gzip_comp_level 6; gzip_proxied expired no-cache no-store private auth; gzip_types text/plain text/xml application/xml application/json application/x-javascript text/javascript text/css;
It should cover most text-based content one will ever serve over the web. Probably.
Header Update
Apparently I forgot to restore original header when migrating the site. I decided to get a new header – an awesome (yuri) (ero)game cg from Hoshizora no Memoria.
To Heart 2 Dungeon Travelers OVA 1
On Comment System
I just migrated to Disqus – a fully managed comment system for websites. I saw it first used in Engadget. It didn’t work quite good at the time (or at least I didn’t have good memory on it) but it’s quite wonderful now.
One of the problem I’m having when leaving comment on other blogs is it’s difficult to track which posts and sites I’ve left a comment on. Some sites (like this site used to be) provide “Notify via E-mail on Replies” option but it’s clunky at best and with dozens, hundreds of sites out there it’s quite impossible to track them all. Not to mention you have to visit each blogs to unsubscribe from notification.
Then come Disqus – it’s a centralized comment system which allows any website to use their service and let the users enjoy one-stop interface to manage all their comments on various websites. It uses JavaScript to embed the comment interface on a page – not the best way but I guess it’s acceptable now with emergence of smartphones and tablets which actually capable of rendering JS.
Replacing WordPress’ comment system with Disqus is quite easy. The official WordPress plugin provides everything to migrate comments quickly and easily. It can even keep the comments synced with local database – allowing quick way out in case Disqus goes evil™.
I doubt anyone still read this blog (and blog is so 2009) but well, here it is.


![[SubSmith] ToHeart2 Dungeon Travelers OVA 01 - Total Disaster [1080p 10bit][76539452].mkv_snapshot_17.32_[2012.03.01_13.32.09]](https://uploads.nanaya.net/wp-content/uploads/sites/2/2012/03/SubSmith-ToHeart2-Dungeon-Travelers-OVA-01-Total-Disaster-1080p-10bit76539452.mkv_snapshot_17.32_2012.03.01_13.32.09-1024x576.jpg)